
Blind Signing: "Fatal" Vulnerability and Web3 Security Strategy
Blind Signing is like signing a digital blank check. This article from Tan Phat Digital will help you understand the attack mechanism and how to set up an optimal security shield for MetaMask wallets and cold wallets.

Why revoke approval doesn't make you 100% safe
Token approval revocation is necessary but vulnerabilities such as private key exposure or sweeper bots still exist. Tan Phat Digital analyzes these limits in depth and how to effectively manage remaining approval risks.

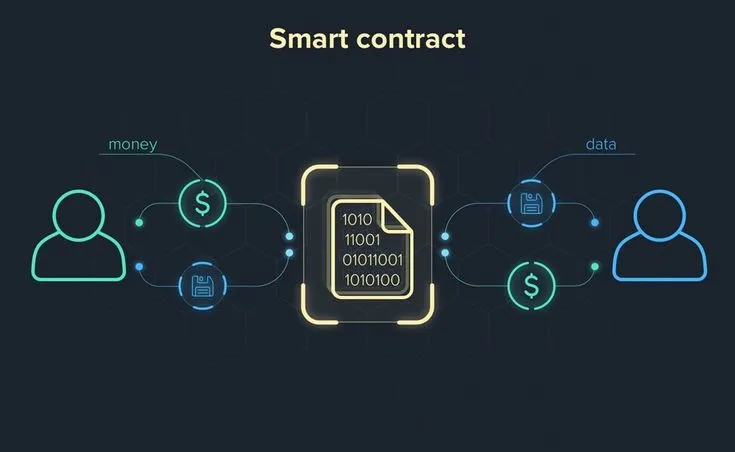
Rug Pull Smart Contract: Effective Identification and Avoidance
Technical analysis of common smart contract vulnerabilities and fraudulent project identification strategies help investors protect assets in the decentralized finance ecosystem.
Why are Smart Contracts without bugs still dangerous?
Even if a Smart Contract has no programming errors, it can still cause billions of dollars in damage due to mistakes in economic design and operational logic. Join Tan Phat Digital in analyzing the boundary between source code safety and system safety.
Read Contract vs Write Contract
A comprehensive view of the operating mechanism of Smart Contract, decoding the harmful confusion between reading and writing data on the chain, and safety instructions from expert Tan Phat Digital.

How dangerous are cross-chain interactive smart contracts?
In-depth analysis report on the most dangerous attack fronts in DeFi: Inter-chain bridges. Learn how hackers exploit huge TVLs and complex logic errors to seize assets.

Signs of Malicious Smart Contracts: Web Security Guide3
In-depth report on the architecture of malicious smart contracts and digital asset security strategies in the risk period of 2026.

Can smart contracts automatically change logic after deployment?
Comprehensive analysis of smart contract variability: from modern Proxy architecture to Metamorphic techniques and secure governance strategies in the blockchain ecosystem.

Hidden Owner Smart Contract: How to Identify & Avoid Backdoors
Discover how developers maintain absolute control through Hidden Owner and risk avoidance techniques for investors from Tan Phat Digital's perspective.

What is Proxy Contract? Risks and How to Avoid Blockchain Fraud
Proxy Contract is the solution for Blockchain's immutability, but is also a loophole for sophisticated scams. The article provides an in-depth analysis of techniques and ways to protect assets.
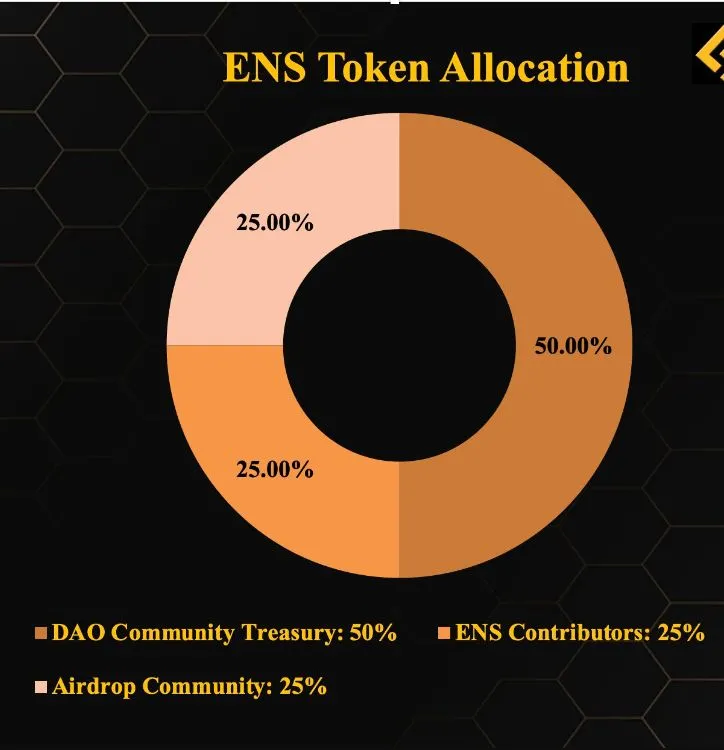
What is Token Allocation? Understand the allocation structure to avoid “junk coins”
Token Allocation is a guideline that helps investors evaluate the transparency and long-term potential of a project. Learn now how to analyze the allocation structure to protect assets with Tan Phat Digital.

What is Impermanent Loss? Silent risks when providing liquidity
Impermanent Loss is a silent risk but has a huge impact on the effectiveness of investment strategies in DeFi. This in-depth analysis will help you understand the mathematical mechanism and how to effectively protect your assets.